A brute pressure assault is an try to achieve entry to a system using successive login makes an attempt. It might be carried out manually or by utilizing an automatic script. In both case, a brute pressure assault tries completely different username and password mixtures with the hope of discovering a sound login.
While brute pressure assaults are simplistic by nature, their implementation is commonly complicated. Since most servers will block a consumer or IP handle after a number of failed logins, a hacker could use a number of methods to carry out a single brute pressure assault. Some assaults could use tons of and even hundreds of gadgets, just like a distributed denial of service DDoS assault.
While the percentages of guessing an accurate login by way of a brute pressure assault are low, it’s nonetheless some of the frequent methods on-line accounts are compromised. Using sufficient makes an attempt, it’s theoretically potential to find any login. However, quick and customary passwords are essentially the most susceptible.
How to Protect Against Brute Force Attacks
The two main methods to guard your on-line accounts from brute pressure assaults are to 1) select sturdy passwords and a pair of) use two-factor authentication.
1. Choose sturdy passwords
A elementary step in securing any on-line account is to decide on a robust password. This means selecting a password that:
- is lengthy – a minimum of eight characters, ideally 12 or more.
- accommodates particular characters – together with numbers and symbols, in addition to lowercase and uppercase characters.
- is just not personally identifiable – using a particular date or the identify of somebody near you makes it straightforward for somebody to manually hack your account.
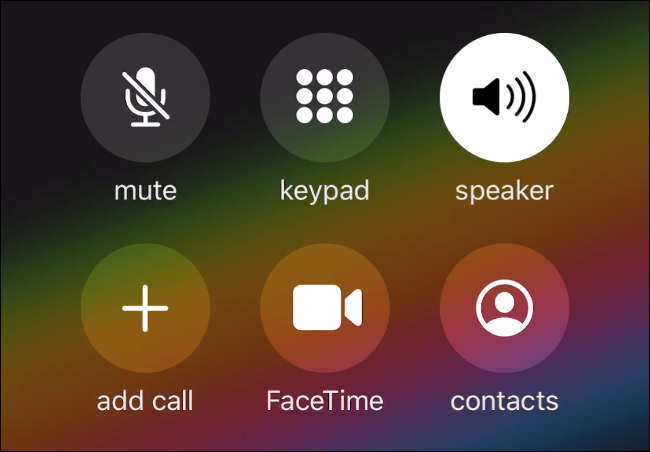
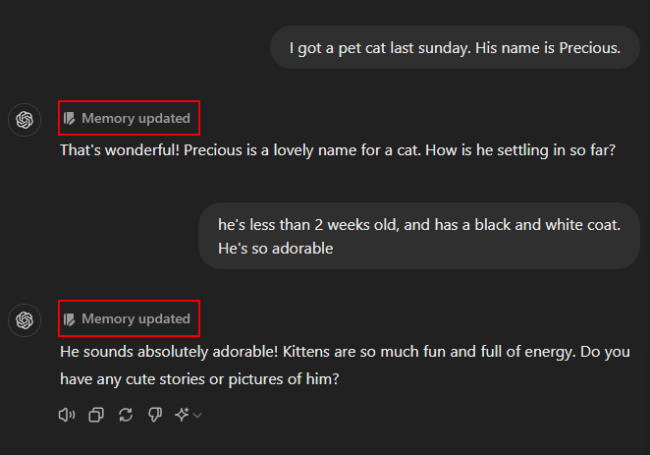
2. Use Two-Factor Identification
Some providers let you allow two-factor authentication, which requires authentication from two gadgets. For instance, you could be requested to enter a username and password in your laptop, adopted by a code despatched by way of textual content to the telephone quantity listed in your account. With two-factor authentication, even when a hacker is aware of your username and password, she or he will be unable to efficiently log in to your account.
Looking to know more Internet Terms









Leave a Reply